Exploring DNS Resolution: The Secret Behind the Internet's Phonebook
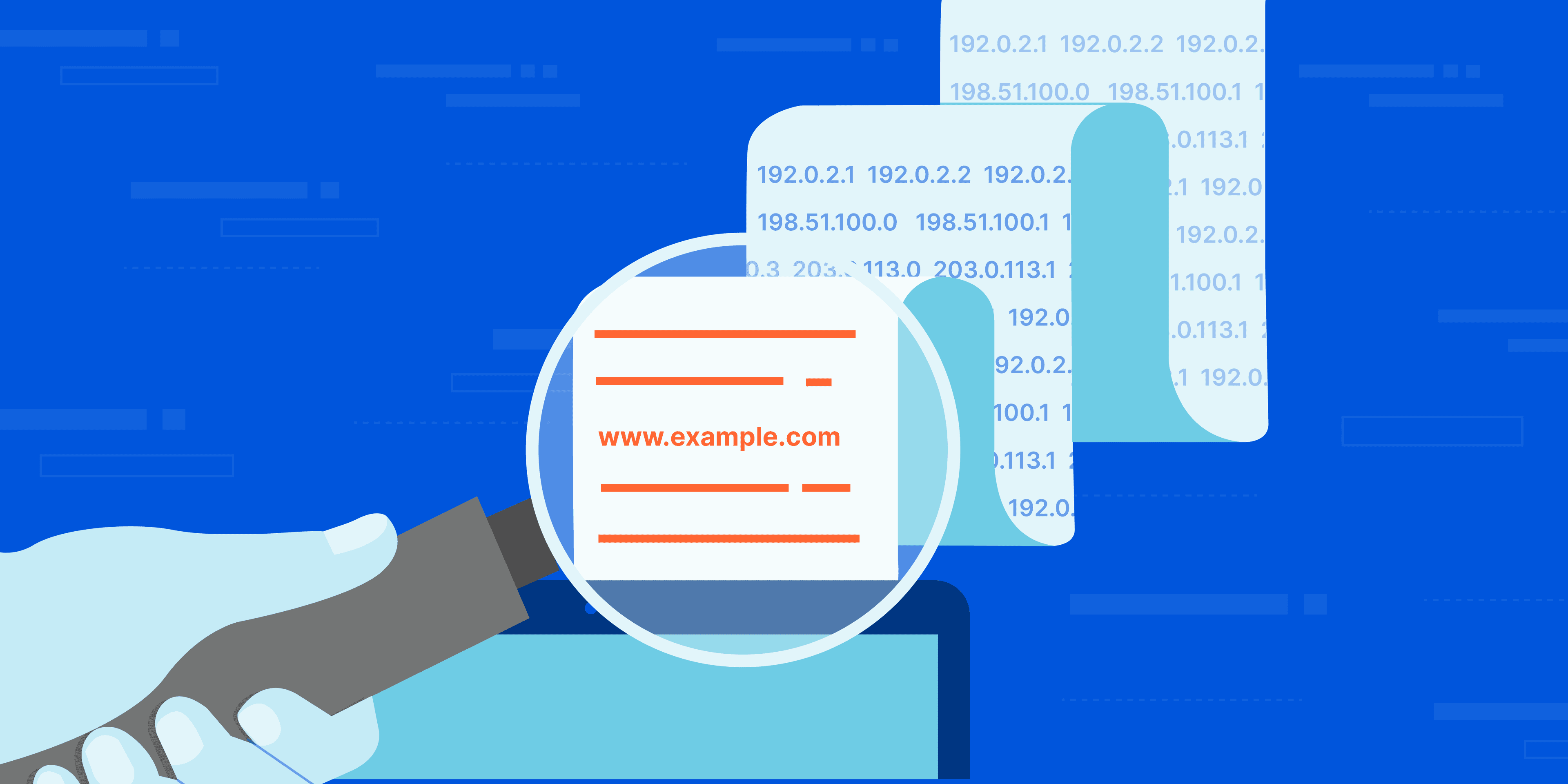
You type google.com into your browser, hit Enter, and within moments, Google's familiar search page appears. It feels like magic, doesn't it? But behind this seemingly instantaneous act lies a sophisticated, distributed system that powers almost every interaction you have with the internet: the Domain Name System, or DNS.
As developers, understanding DNS isn't just a "nice to know"; it's crucial for diagnosing network issues, configuring domains, and building robust applications. In this article, we'll peel back the layers of DNS resolution, using practical examples and a powerful command-line tool called dig, to understand how the internet's "phonebook" truly operates.
What is DNS and Why Do We Need It?
Imagine trying to remember the phone number of every single person you know. Difficult, right? Now imagine trying to remember the IP address (like 172.217.160.142) for every single website on the internet. It would be impossible!
This is where DNS comes in. Just like a phonebook maps names to phone numbers, DNS maps human-readable domain names (like google.com or hashnode.com) to machine-readable IP addresses.
Why is this essential?
Human Usability: Domain names are easy to remember and type.
Flexibility: IP addresses for websites can change for various reasons (server migrations, load balancing), but the domain name remains constant. DNS handles the update seamlessly.
Scalability: It's a distributed system designed to handle billions of queries every day.
Without DNS, the internet as we know it simply wouldn't function.
Introducing dig: Your DNS Detective Tool
Before we dive into the mechanics, let's meet our investigative partner: dig (Domain Information Groper). This command-line utility is indispensable for anyone wanting to debug or understand DNS queries.
What is dig?
dig is a flexible tool for querying DNS name servers. It allows you to directly ask DNS servers for information about domain names, such as their IP addresses, mail servers, or name servers.
Why do developers use it?
Direct Interaction: Unlike your browser, which hides DNS resolution,
digshows you the raw responses from DNS servers.Verification: You can check if your domain's DNS records are configured correctly and have propagated across the internet.
Troubleshooting: If a website isn't loading,
digcan help determine if it's a DNS issue (e.g., incorrect IP address, name server not responding).
When is it useful for debugging DNS issues?
After changing domain name servers or IP addresses.
When a new website isn't reachable.
When email isn't being delivered to your domain (checking MX records).
To understand exactly which DNS server is providing a specific answer.
To use dig, simply open your terminal and type dig followed by the domain name. For example:
dig google.com
The Layered World of DNS Resolution: A Hierarchy of Servers
DNS isn't a single, monolithic server. It's a vast, distributed database organized in a strict hierarchy. Think of it like a global directory system where different "phonebooks" are responsible for different sections.
The resolution process involves several types of specialized DNS servers, each with a distinct role:
DNS Resolver (or Recursive Resolver): This is typically operated by your Internet Service Provider (ISP) or a public service like Google DNS (8.8.8.8) or Cloudflare (1.1.1.1). When your computer needs to find an IP address, it sends the query to a recursive resolver. This resolver then does all the legwork to find the answer.
Root Name Servers: These are at the very top of the DNS hierarchy. There are 13 logical root servers globally (though many more physical instances). They know where to find the TLD name servers.
TLD (Top-Level Domain) Name Servers: These servers are responsible for domains ending in common suffixes like
.com,.org,.net, or country codes like.uk,.de. They know which authoritative name servers are responsible for specific domain names within their TLD.Authoritative Name Servers: These are the final authority for a specific domain (e.g.,
google.com). They hold the actual DNS records (like the IP address) for that domain and its subdomains.
You can visualise this hierarchy:

Step-by-Step Resolution with dig
Let's walk through the DNS resolution process using dig commands, understanding what each step reveals about the hierarchy.
1. The Apex of the Internet: Root Name Servers
Every DNS query begins, conceptually, at the root. The root name servers know where to find the servers responsible for the top-level domains.
To query the root name servers, we use . (a single dot) as the domain name and ask for NS (Name Server) records.
dig . NS
What NS records are: An NS (Name Server) record indicates which DNS servers are authoritative for a particular domain or a zone. They are crucial for delegating authority within the DNS hierarchy. When a server returns an NS record, it's essentially saying, "I don't have the answer you're looking for, but these servers might. Go ask them!"
Example Output (truncated for clarity):
; <<>> DiG 9.10.6 <<>> . NS
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 6226
;; flags: qr rd ra; QUERY: 1, ANSWER: 13, AUTHORITY: 0, ADDITIONAL: 26
;; QUESTION SECTION:
;. IN NS
;; ANSWER SECTION:
. 85449 IN NS a.root-servers.net.
. 85449 IN NS b.root-servers.net.
. 85449 IN NS c.root-servers.net.
... (10 more root servers listed) ...
;; Query time: 1 msec
;; SERVER: 192.168.1.1#53(192.168.1.1)
;; WHEN: Sat Jan 31 10:15:43 2026
;; MSG SIZE rcvd: 520
The ANSWER SECTION shows the 13 root name servers (e.g., a.root-servers.net, b.root-servers.net). These servers are not the "final answer" for google.com; they tell us who to ask next if we're looking for a .com domain.
2. Navigating Top-Level Domains (TLDs)
Next, the recursive resolver (or you, using dig) would ask one of the root servers: "Where can I find .com domains?" The root server would respond with the NS records for the .com TLD servers.
Let's query the .com TLD name servers for their NS records:
dig com NS
Example Output (truncated):
; <<>> DiG 9.10.6 <<>> com NS
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 36724
;; flags: qr rd ra; QUERY: 1, ANSWER: 13, AUTHORITY: 0, ADDITIONAL: 26
;; QUESTION SECTION:
;com. IN NS
;; ANSWER SECTION:
com. 172800 IN NS j.gtld-servers.net.
com. 172800 IN NS k.gtld-servers.net.
com. 172800 IN NS l.gtld-servers.net.
... (10 more TLD servers listed) ...
;; Query time: 2 msec
;; SERVER: 192.168.1.1#53(192.168.1.1)
;; WHEN: Sat Jan 31 10:15:43 2026
;; MSG SIZE rcvd: 520
Now we have a list of .com TLD name servers (e.g., j.gtld-servers.net). These servers are responsible for knowing which specific authoritative name servers handle each domain ending in .com. They still don't have Google's IP address, but they know who does.
3. Finding the Source: Authoritative Name Servers
With the .com TLD servers identified, the next step is to ask one of them: "Who is authoritative for google.com?"
Let's query for the NS records of google.com:
dig google.com NS
Example Output:
; <<>> DiG 9.10.6 <<>> google.com NS
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 3959
;; flags: qr rd ra; QUERY: 1, ANSWER: 4, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;google.com. IN NS
;; ANSWER SECTION:
google.com. 259200 IN NS ns1.google.com.
google.com. 259200 IN NS ns2.google.com.
google.com. 259200 IN NS ns3.google.com.
google.com. 259200 IN NS ns4.google.com.
;; Query time: 3 msec
;; SERVER: 192.168.1.1#53(192.168.1.1)
;; WHEN: Sat Jan 31 10:15:43 2026
;; MSG SIZE rcvd: 161
The ANSWER SECTION now lists the authoritative name servers for google.com (e.g., ns1.google.com, ns2.google.com). These are Google's own DNS servers, and they are the final source of truth for all records related to google.com, including its IP address.
4. The Grand Finale: Full DNS Resolution
Finally, we're ready to ask an authoritative server for the actual IP address of google.com. When you simply run dig google.com, your recursive resolver performs all the steps above behind the scenes and returns the answer.
dig google.com
Example Output (truncated):
; <<>> DiG 9.10.6 <<>> google.com
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 6365
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1
;; QUESTION SECTION:
;google.com. IN A
;; ANSWER SECTION:
google.com. 264 IN A 172.217.160.142
;; AUTHORITY SECTION:
;; (empty)
;; ADDITIONAL SECTION:
;; (empty)
;; Query time: 10 msec
;; SERVER: 192.168.1.1#53(192.168.1.1)
;; WHEN: Sat Jan 31 10:15:43 2026
;; MSG SIZE rcvd: 55
The ANSWER SECTION finally gives us what we were looking for: an A record (Address record) that maps google.com to the IP address 172.217.160.142. This is the IP address of one of Google's web servers.
Summary of the dig progression:
| dig Command | What it queries | What it finds (NS records) |
dig . NS | Root Name Servers | Addresses of TLD name servers |
dig com NS | TLD name servers for .com | Addresses of authoritative name servers for .com |
dig google.com NS | Authoritative name servers for google.com | Addresses of google.com’s own NS servers |
dig google.com | Authoritative name server for google.com | The actual A record (IP address) for google.com |
The Role of Recursive Resolvers
While we used dig to simulate the step-by-step process, in reality, your browser doesn't go through this journey itself. That's the job of the recursive resolver.
Here's how it typically works:
When you type
google.com, your browser first checks its own cache to see if it already knows the IP address.If not found, it asks your operating system (OS).
The OS checks its own cache.
If still not found, the OS sends a query to the recursive resolver it's configured to use (your ISP's DNS server, or one you manually set like 8.8.8.8).
The recursive resolver then starts the full lookup process:
It asks a Root Name Server for the
.comTLD servers.It asks a TLD Name Server for the authoritative name servers for
google.com.It asks an Authoritative Name Server for the IP address of
google.com.
Once the recursive resolver gets the IP address (e.g.,
172.217.160.142), it caches this information for a period (determined by the record's TTL - Time To Live) to speed up future requests.The recursive resolver sends the IP address back to your OS.
Your OS sends it back to your browser.
Finally, your browser now has the IP address and can establish a connection to
172.217.160.142to request the webpage.
This interaction ensures that your device only needs to know about one DNS server (the recursive resolver), offloading the complex, multi-step lookup process to a specialized service.

Connecting dig Output to Browser Behavior
When you run dig google.com and see google.com. 264 IN A 172.217.160.142 in the ANSWER SECTION, you're seeing the exact piece of information that your recursive resolver eventually provides to your browser.
The 264 is the TTL (Time To Live) in seconds, meaning this specific answer should be cached for 264 seconds before being considered "stale" and requiring a fresh lookup.
Once your browser receives 172.217.160.142, it then initiates a standard HTTP request to that IP address on port 80 (for HTTP) or 443 (for HTTPS). The web server at that IP address responds with the webpage content, and voilà, google.com loads!
Conclusion
DNS resolution is a cornerstone of the internet, a marvel of distributed system design that allows us to navigate the web with ease. From the global Root Name Servers to the specific Authoritative Name Servers for each domain, it's a carefully orchestrated dance of delegation and query forwarding.
As developers, understanding this process — especially with a tool like dig empowers you to diagnose problems, make informed infrastructure decisions, and truly grasp how your applications are delivered to users around the globe. So, the next time you type a URL, remember the intricate journey your request takes through the internet's phonebook to bring that website to your screen!